
Key Takeaways
- Google classifies cybersecurity as YMYL, applying the same E-E-A-T scrutiny it gives healthcare and finance. Rankings require editorial validation from publications search engines already trust — not volume from generic blogs.
- The cybersecurity news cycle never stops. Every breach, zero-day, and regulatory change creates journalist demand for expert commentary — making reactive digital PR the highest-ROI authority-building tactic in the security vertical.
- Ransomware appeared in 44% of breaches in the 2025 Verizon DBIR, up from 32% the prior year. Every one of those incidents generated a media cycle where security journalists needed credentialed sources. That's the link building opportunity.
- AI search engines are cautious about security recommendations. The cybersecurity brands they cite are the ones with the deepest editorial footprint across Dark Reading, SecurityWeek, CSO Online, and similar publications — not the ones with the most content.
- Global cybersecurity spending is projected to reach $240 billion in 2026. The companies capturing that budget are researching solutions through search and AI tools months before they talk to sales. If you're invisible there, you're invisible.
Cybersecurity SEO is a different animal. The market is crowded with enterprise vendors who've been accumulating press coverage for decades, the audience is technically sophisticated enough to spot shallow content from a mile away, and Google applies YMYL-level scrutiny to every security-related page it indexes.
That last part is what makes the cybersecurity vertical uniquely challenging — and uniquely suited to digital PR as an authority-building strategy. When search engines require third-party editorial validation before they'll rank your content, the playbook shifts from "create more content" to "earn coverage from the publications your buyers already read."
This guide covers the cybersecurity SEO strategy that actually works in a YMYL landscape: building editorial authority through the security media ecosystem, positioning credentialed experts as journalist sources, and turning the constant stream of breaches and vulnerability disclosures into ranking signals.
Why Cybersecurity SEO Is Harder Than You Think
Cybersecurity falls under Google's YMYL classification — the same scrutiny tier as healthcare and financial services. Inaccurate security advice can compromise user data and digital safety, so the algorithm demands stronger proof of expertise before it will rank your content.
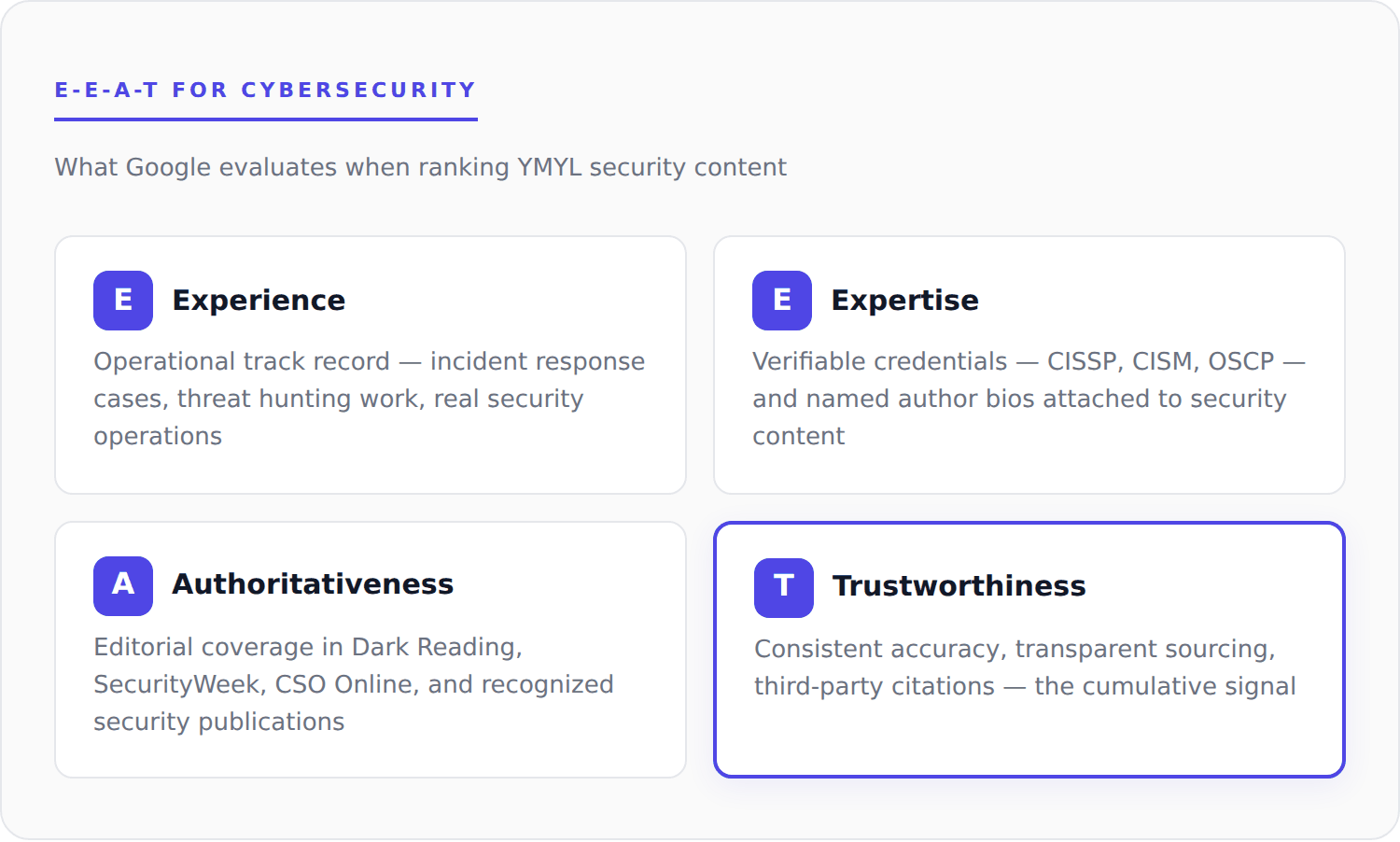
"Your Money or Your Life" is Google's classification for content that can affect a reader's safety, finances, or wellbeing. YMYL pages are held to a higher E-E-A-T bar — Experience, Expertise, Authoritativeness, and Trustworthiness — which in practice means search engines weight third-party editorial validation more heavily than they do for non-YMYL content.
In practice, YMYL classification creates three structural realities for cybersecurity content:
- The authority bar is higher. Links from generic blogs barely register. Google needs to see recognized security and technology publications vouching for your expertise before it trusts your content enough to rank it.
- The competition is well-funded. CrowdStrike, Palo Alto Networks, and Mandiant have decades of press coverage baked into their link profiles. You can't outpublish them — but you can out-credential them on specific topics where your experts have deeper operational knowledge.
- AI search adds another layer. ChatGPT, Perplexity, and Google AI Mode are even more cautious than traditional search about recommending security products. The brands they cite are the ones with consistent editorial coverage across multiple trusted publications — not the ones with the biggest content library.
| Content tier | Authority required | What Google needs to see |
|---|---|---|
| Standard SEO | Moderate | Content quality and topical relevance often sufficient for ranking |
| YMYL Finance | High | Credentialed authors, editorial citations, recognized publication backlinks |
| YMYL Cybersecurity | Very high | Editorial validation from security press, credentialed experts, consistent third-party sourcing |
IBM's 2025 Cost of a Data Breach Report found that U.S. breach costs hit a record $10.22 million — up 9% year-over-year while global costs actually declined. Every one of those incidents generated media coverage where journalists needed credentialed expert sources. The cybersecurity media ecosystem produces link building opportunities at a pace no other industry matches.
Why Digital PR Is the Natural Fit
Digital PR works in cybersecurity because the news cycle never stops generating opportunities for credentialed expert commentary — exactly the editorial validation YMYL algorithms require.
Most industries have to manufacture reasons for journalists to cover them. Cybersecurity doesn't have that problem. Ransomware appeared in 44% of breaches in the latest Verizon DBIR, up from 32% the prior year. Stolen credentials were the initial access vector in 22% of breaches. Every single one of those incidents generated articles where security journalists needed experts who could assess the attack vector, explain the implications, and advise on response.
That's the structural advantage. The news never stops, and the journalists covering it have strict sourcing standards that favor credentialed security professionals over marketing teams. When your CISO or head of threat research provides commentary on a high-profile breach, the resulting coverage builds exactly the editorial authority that YMYL algorithms demand.
Beyond reactive opportunities, digital PR for link building works in cybersecurity for three reasons:
- Editorial links are the trust signal Google needs. When Dark Reading or SecurityWeek features your expert's analysis, that's the kind of third-party endorsement YMYL content needs to rank. A hundred guest posts on generic marketing blogs won't move the needle the way a single earned placement in SC Magazine does.
- Brand mentions build AI visibility. AI search systems recommend the brands they see most frequently across trusted sources. Every editorial mention — even unlinked — strengthens your citation potential in ChatGPT, Perplexity, and AI Overviews.
- Your technical expertise is the moat. A generalist PR agency can't provide expert commentary on a zero-day vulnerability in Ivanti Connect Secure. Your threat researchers can. That specificity is what makes pitches land and what competitors can't easily replicate.
Where Cybersecurity Links Actually Come From
Not all publications carry equal weight in cybersecurity SEO. The ones that matter fall into three tiers based on how search engines and AI systems value them.
| Tier | Examples | DR range | Why it matters |
|---|---|---|---|
| Tier 1 — Security-specific | Dark Reading, SecurityWeek, CSO Online, SC Magazine, Infosecurity Magazine, The Hacker News | DR 70+ | Read daily by CISOs and SOC managers; primary sources AI systems pull from for security recommendations |
| Tier 2 — Tech with security desks | TechCrunch, Wired, Ars Technica, ZDNet, Forbes, VentureBeat | DR 80+ | Combine high domain authority with broader reach; reach security community and the C-suite simultaneously |
| Tier 3 — Vertical and compliance | HIPAA Journal, Bank Info Security, FedScoop, Compliance Week | DR 50–75 | Strong topical relevance for industry-specific positioning; lower DR but higher contextual authority |
Tier 1 carries the most weight for both YMYL trust and AI citation. Tier 2 broadens reach to non-security buyers and decision-makers. Tier 3 is where vertical-specific authority gets built — essential when targeting industries like healthcare or financial services. For broader context on tech media strategy, see our technology link building guide.
Pitches from CISSPs, CISMs, former CISOs, and active threat researchers consistently outperform pitches from marketing teams. If your company has credentialed security professionals, they're your most valuable PR asset. Lead with the expert, not the product.
5 Strategies That Build Real Authority
Five tactics consistently produce the editorial coverage that moves YMYL rankings. They're listed in rough order of ROI, but the right mix depends on your team's expertise, your data assets, and how fast your approval process moves.
1. Breach and vulnerability newsjacking
This is the single highest-ROI tactic in cybersecurity SEO. When a breach hits the news, journalists have hours — sometimes less — to produce analysis. They need credentialed experts who can explain the attack vector, assess the blast radius, and advise on containment. One well-timed response to a major incident can earn 5-10 editorial placements in a single news cycle.
The key is speed. A breach creates a 24-48 hour window. If your approval process for press commentary takes a week, you'll miss every opportunity. Pre-approved expert bios, templated perspectives on common attack categories (ransomware, supply chain compromise, credential theft), and a fast-track legal review process are the operational foundation.
High-value newsjacking triggers: major data breaches, zero-day vulnerability disclosures, ransomware incidents affecting critical infrastructure, new SEC cyber disclosure requirements, and vendor security advisories.

2. Original threat intelligence reports
Companies that publish original threat research become the source every subsequent article cites. Annual threat landscape reports, breach trend analyses, and incident response benchmarks create linkable assets that compound for years.
If your SOC tracks threat patterns, that aggregate data — anonymized — is exactly what journalists need for trend stories. When you own the data, you own the citations. The Verizon DBIR gets linked thousands of times annually for exactly this reason. You don't need that scale, but even a focused report on your vertical's specific threat landscape (ransomware trends in healthcare, credential theft patterns in financial services) creates a persistent source that earns links organically.
3. Expert commentary through journalist platforms
Security journalists on platforms like Qwoted, Featured, and other journalist sourcing services post queries daily. Topics range from zero-trust architecture to AI-driven threats to compliance frameworks. Your CISO or threat research lead responds with specific, quotable commentary — not a marketing pitch. Lead with the insight, not the brand.
4. Compliance and regulatory commentary
Every new regulation creates a coverage wave. SEC cyber disclosure rules, NIS2, state-level privacy laws, updated PCI DSS requirements — each generates articles needing credentialed sources. This is an evergreen pipeline. The brands that consistently comment on compliance build journalist relationships that pay compounding dividends across their entire link profile.
5. Targeted link insertions for solution pages
While digital PR builds domain-wide authority, link insertions place links on existing articles — security tool comparisons, best-of lists, and technical guides already ranking for your target terms. This is how you direct authority to specific product and solution pages rather than just your homepage. Target DR 60+ sites in the security or technology vertical.
| Strategy | ROI profile | Best for |
|---|---|---|
| Breach newsjacking | Highest immediate ROI | Companies with credentialed experts and fast approval workflows |
| Threat intelligence reports | Compounding (years of citations) | Companies with SOC data, MDR telemetry, or research teams |
| Expert commentary platforms | Consistent steady output | Any company with a CISO or named security expert available for outreach |
| Regulatory commentary | Evergreen pipeline | Compliance-focused vendors and GRC platforms |
| Targeted link insertions | Page-level authority routing | Specific product or solution pages that need direct authority |
Nightfall, an AI-native DLP platform, grew organic traffic 287% in 13 months through 57 targeted link insertions averaging DR 72. Each placement was selected for topical fit across cybersecurity, cloud computing, and SaaS technology sites — directing authority to specific product and blog pages.
Cybersecurity SEO by Subcategory
The strategy shifts depending on what kind of security company you are. An MSSP targeting SMBs has different publication targets and keyword priorities than an enterprise zero-trust vendor.
| Subcategory | Highest-impact tactics | Priority publications |
|---|---|---|
| MSPs / MSSPs | SMB threat research reports, compliance readiness surveys, local and regional coverage | ChannelE2E, CRN, MSSP Alert |
| Enterprise security | Breach analysis commentary, zero-trust thought leadership, CISO positioning as expert source | Dark Reading, CSO Online, SecurityWeek |
| Cloud security | Misconfiguration research, multi-cloud benchmark data, shared responsibility analysis | The New Stack, InfoWorld, SC Magazine |
| GRC / Compliance | Regulatory newsjacking (SEC, NIS2, PCI DSS), compliance survey data, audit-focused content | Compliance Week, Risk.net, HIPAA Journal |
| Identity / Access | Zero-trust adoption research, authentication trend data, credential theft commentary | Dark Reading, VentureBeat, Wired |
AI Search and Cybersecurity Discovery
Security buyers are already using AI tools to research solutions before they ever talk to sales. Questions like "best SIEM platforms for mid-market," "MDR vs. MSSP comparison," and "how to choose a penetration testing vendor" increasingly start in ChatGPT and Perplexity rather than Google.
Three things make AI visibility critical specifically for cybersecurity:
- Security purchases involve extensive research. Cybersecurity buyers engage with 13+ content assets on average before making a decision, according to ActualTech Media research — higher than most industries. Only 25% of buyers can assemble budget within six months (FutureB2B 2025 Cybersecurity Buyers Guide). If AI tools recommend your competitors during that research window, you've lost the deal before your sales team gets involved.
- AI applies extra caution to security recommendations. Just like with health and financial advice, AI systems hold security product recommendations to a higher bar. They default to brands with the broadest editorial footprint across recognized security publications — not the ones with the best content marketing.
- Coverage breadth matters more than depth. A single viral article won't sustain AI citations. Consistent mentions across Dark Reading, SecurityWeek, TechCrunch, and vertical publications create the pattern AI systems rely on. For deeper strategies, see our AI search optimization guide.
| What AI systems trust | What doesn't move the needle |
|---|---|
| Editorial coverage in recognized security publications | Volume of self-published blog content |
| Named expert sources with verifiable credentials | Guest posts on generic marketing sites |
| Consistent brand mentions across multiple outlets | Paid placements or sponsored content |
| Original research cited by journalists | Press releases without earned follow-up coverage |
Mistakes That Kill Cybersecurity SEO Programs
Five operational mistakes consistently undermine cybersecurity link building programs — most of them avoidable with the right setup.
- Leading with product marketing instead of threat expertise. Security journalists reject vendor pitches. They want analysis of the attack, not a product demo. Every pitch should lead with the expert's assessment, not your solution's features.
- Missing the news cycle window. A breach creates a 24-48 hour window for expert commentary. If your legal review takes five business days, you'll consistently lose to competitors with pre-approved processes in place. This is the single most common operational failure.
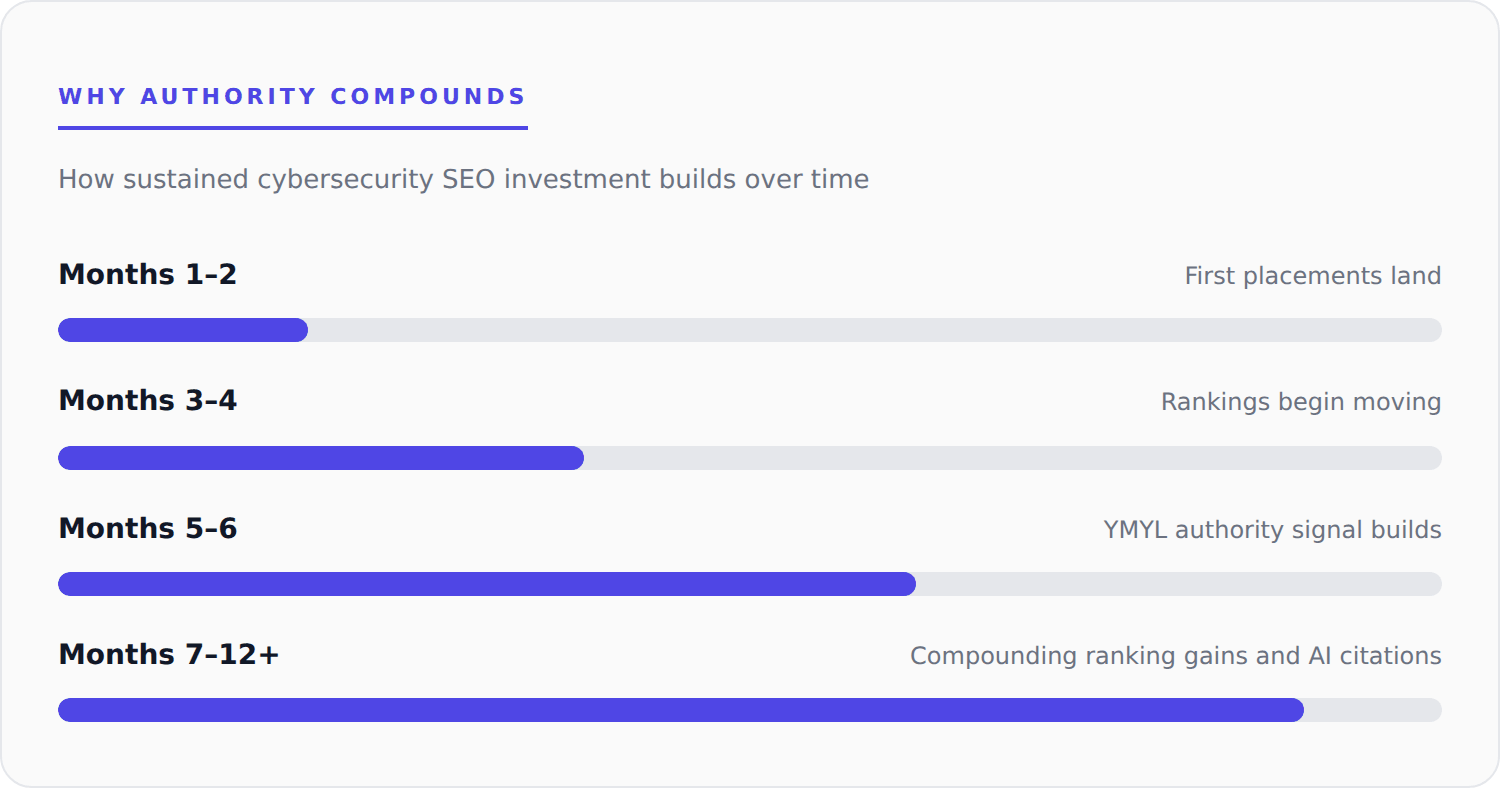
- Treating link building as a campaign instead of a program. Three months of effort followed by silence doesn't build the sustained authority YMYL algorithms reward. Cybersecurity SEO compounds — six months of consistent editorial coverage produces exponentially more ranking impact than six months of sporadic effort. See our timeline guide for realistic expectations.
- Targeting only business media. CISOs read different publications than CFOs. If you're only pursuing Forbes and Bloomberg, you're missing the practitioner audience that influences purchasing decisions. Delinea research found that IT Operations teams have the final say in 38% of cybersecurity purchases — more than the CISO and security team combined (32%).
- Publishing research without expert attribution. Anonymous threat reports don't satisfy E-E-A-T. Named authors with verifiable credentials (CISSP, CISM, OSCP) carry significantly more weight with both journalists and search algorithms. Put names and credentials on everything.
Budget and Timeline Expectations
Cybersecurity SEO requires sustained investment because YMYL classification penalizes inconsistency — but the unit economics are favorable given the CPCs in this vertical.
| Dimension | Benchmark | Why |
|---|---|---|
| Monthly investment | $5,000 – $12,000+ | YMYL competition requires consistent quality output |
| Target publication DR | DR 60+ | Security publications tend to carry high authority |
| Time to first placements | 2–4 weeks | Reactive opportunities accelerate this when news cycles cooperate |
| Time to ranking impact | 4–6 months | YMYL niches respond more slowly than non-YMYL verticals |
| Minimum commitment | 6 months | Needed for compounding authority effects to materialize |
Cybersecurity keywords carry CPCs of $15-$75+ in Google Ads, with enterprise terms regularly exceeding $100 per click. Every organic ranking you earn replaces paid traffic at those rates, and the authority compounds as your editorial footprint grows. For detailed cost breakdowns, see our link building pricing guide.
Getting Started
Five steps to set up a cybersecurity SEO program that compounds:
- Audit your link profile. Check your referring domain count and DR distribution in Ahrefs or Semrush. Compare against the competitors ranking above you to quantify the authority gap. Our link audit guide walks through the process.
- Identify your credentialed experts. Who holds CISSP, CISM, CEH, or OSCP certifications? Who has deep expertise in specific threat areas? These people are your primary spokespeople for earned media. Build author bios and headshots — journalists need these ready to go.
- Build a rapid-response process. Pre-approved expert bios, templated commentary on common attack types, and a fast-track approval workflow. When the next breach hits, you need to respond within hours, not days.
- Inventory your data assets. What proprietary threat data, incident response benchmarks, or compliance readiness metrics could you publish as original research? That data is what earns links that compound.
- Talk to a specialist. A 15-minute call can identify your highest-impact opportunities based on your current authority profile and competitive landscape. Start here.
Build Authority in Cybersecurity.
Free competitive analysis showing which publications to target for maximum ranking impact.
Frequently Asked Questions
Why is cybersecurity SEO harder than other industries?
YMYL classification means Google demands third-party editorial proof before ranking security content. You're also competing against enterprise vendors with decades of accumulated press coverage, and your audience of security professionals will immediately recognize shallow content. It's a vertical where expertise can't be faked.
Do we need credentialed security professionals for this to work?
Credentials dramatically improve placement rates with security journalists, who have strict sourcing standards. If your team includes CISSPs or certified threat researchers, they should be the face of your media outreach. Companies without certified staff can still earn coverage through original data and threat research, but credentialed experts shorten the path considerably.
How fast can we get placements after a major breach?
With pre-built assets and a rapid-response workflow, 24-72 hours is realistic. The bottleneck is almost always internal approval speed. Companies with pre-approved bios and templated commentary frameworks respond fastest and win the most placements.
Which types of security companies benefit most from this approach?
The strategy applies across the cybersecurity vertical — MSSPs, enterprise security vendors, cloud security platforms, identity providers, GRC tools, and consulting firms. The specific publications and angles shift by subcategory, but the core mechanism (editorial authority from trusted security media) works the same way.
What ROI should we expect?
Security keywords carry some of the highest CPCs in all of paid search — $15-$75+ per click, with enterprise terms exceeding $100. Every organic ranking replaces paid spend at those rates. The authority also compounds: six months of consistent coverage builds a link profile that keeps producing ranking improvements even after the initial investment. For the full framework, see our link building ROI guide.
How is this different from traditional cybersecurity PR?
Traditional PR focuses on brand awareness and analyst relations. Digital PR optimizes for measurable SEO outcomes — backlinks and brand mentions that improve rankings and AI visibility. The tactics overlap (journalist relationships, expert positioning), but digital PR connects directly to search performance metrics. For agencies offering this to security clients, we provide white-label fulfillment.
Sources
- IBM — Cost of a Data Breach Report 2025
- Verizon — 2025 Data Breach Investigations Report (DBIR)
- Gartner — Worldwide Cybersecurity Spending Forecast 2026
- ActualTech Media — Cybersecurity Buyer Content Engagement Research (2025)
- FutureB2B — 2025 Cybersecurity Buyers Guide
- Delinea — IT Decision Maker Cybersecurity Purchase Research

Brandon founded Reporter Outreach in 2017. Since then, he and his team have run 500+ editorial link building campaigns for healthcare, SaaS, technology, and more, earning over 25,000 placements. He writes about digital PR, link building, and how authority signals are shifting for AI search.




